Is Manufacturing Technology in Industry 4.0 or Industry 5.0?

Navigating the Next Frontier of Manufacturing Technology Manufacturing technology is constantly evolving. Industry leaders have an array of innovations to keep up with. You have likely heard discussion of Industry 4.0 and Industry 5.0, but which era are we in? Which of these matter most for your business? This question is not just a matter […]
CMMC Compliance: Everything You Need to Know Now

Please note: CPE was only available for the live version of this event. CPE is not available for webinars on demand. In this webinar, the experts at Clark Schaefer Consulting (a Registered Practitioner Organization), will share their expertise and cover the things you need to know now to avoid costly issues in the future. Hear […]
4 Key Benefits of a Cybersecurity Live Fire Exercise

Every business faces threats to their cybersecurity and, hopefully, has a variety of policies and procedures in place to keep them safe. How do you know if your safeguards are reliable? How can you ensure that your employees are following the policies as intended and executing the necessary steps if you are faced with a […]
NYDFS Cybersecurity Checklist
Are you prepared for the amended NYDFS cybersecurity regulation to take effect? The comment period ended on January 9, 2023, so the changes are coming. The proposed amendment includes many new requirements that span all areas of cybersecurity. We’ve put together the following NYDFS cybersecurity checklist so you can assess your readiness to comply. Some […]
Navigating the New Data Privacy Landscape
Over the last two years, the way we live and work has changed dramatically. As the world moved into various stages of lockdown, we became more reliant on digital platforms for everything from work meetings to grocery shopping to hanging out with friends. This increased online presence has given rise to significant concerns about the […]
Don’t Be a Victim of Construction Fraud

The sudden awareness you’ve been defrauded happens in an instant: it’s an email from a coworker asking why a large capital outlay occurred or a spelling error that you notice in a vendor’s name. Even worse, it could be a voicemail from the state Attorney General’s office. That sinking feeling is all too familiar to […]
Infographic: 7 Reasons to increase Your Cybersecurity Budget
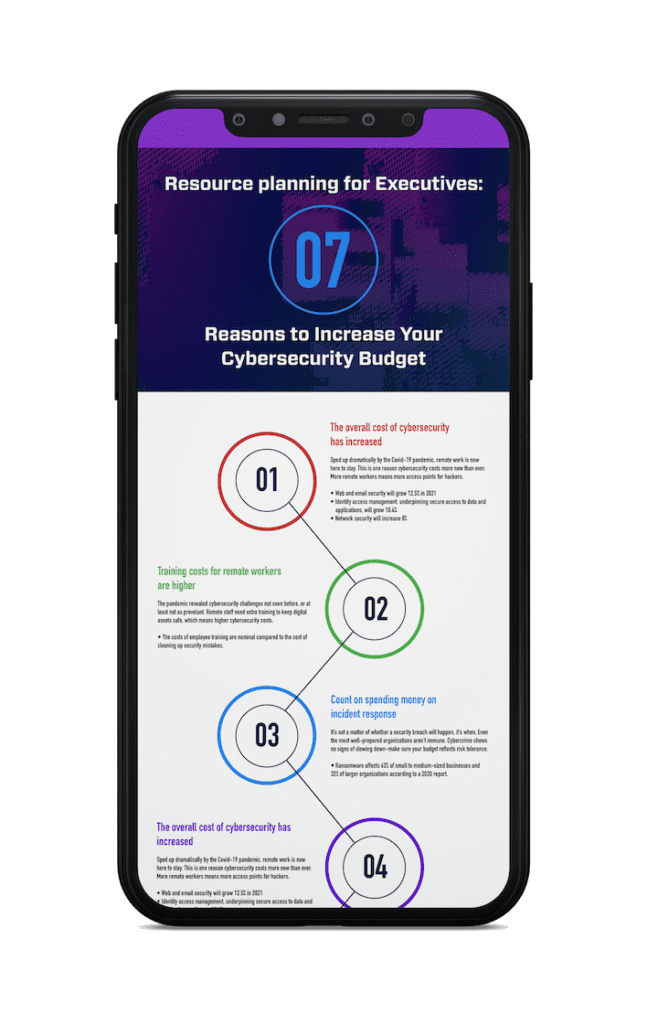
Download the infographic as a PDF
Infographic: 7 Common Behaviors That Make Your Company an Easy Target

Download the infographic as a PDF
4 Benefits of Custom Software Applications

Saving money and driving efficiencies are top priorities for nearly every business. One way companies are accomplishing this is through automation and the adoption of new digital tools that can be tailored to the organization’s needs. Custom software development, also known as custom application development, is the creation of software applications for specific workflows within […]
Strained VPN capacity: a must-solve with a remote workforce

More than a year into the Covid-19 pandemic, a large part of the workforce continues to operate in a remote setting. All signs indicate that remote work is here to stay due in part to the benefits technology provides—but is your network capable of handling users from multiple settings? Some organizations still grapple with the […]
